Zero Trust sounds elegant in theory: trust no one, verify everything, secure the enterprise. In practice? It's a labyrinth, complex, disorienting, and unforgiving if you misstep. I saw this firsthand while working with the Cybersecurity and Infrastructure Security Agency (CISA) on their freshly released Zero Trust Maturity Model 2.0, unveiled January 30, 2022. As a Program Management Specialist at the Technology Modernization Fund (TMF) under GSA, I partnered with CISA to align their framework with updated OMB mandates, like Memorandum M-22-09—and applied it to assess cybersecurity proposals vying for TMF's $1 billion pool. This post unpacks that journey: decoding Zero Trust, spotlighting CISA's pillars, and revealing why TMF became a lifeline for agencies racing to modernize beyond the sluggish appropriations cycle.
Setting the Stage: A Zero Trust Reckoning
By early 2022, federal cybersecurity was at a crossroads. The May 2021 Executive Order 14028 had sounded the alarm, modern threats demanded a shift from perimeter-based defenses to Zero Trust Architecture (ZTA). OMB's subsequent mandates doubled down, setting aggressive timelines. At TMF, where I'd spent two years streamlining IT modernization, we saw a surge in ZTA-focused proposals. Agencies needed funding fast, normal budget cycles couldn't keep pace with ransomware spikes or nation-state hacks. Enter CISA's 2.0 model: a roadmap to guide agencies through the maze. I joined their working group to bridge policy and practice, leveraging my TMF lens to ensure it wasn't just theory but a tool we could wield.
CISA's Five Pillars: The Technical Backbone
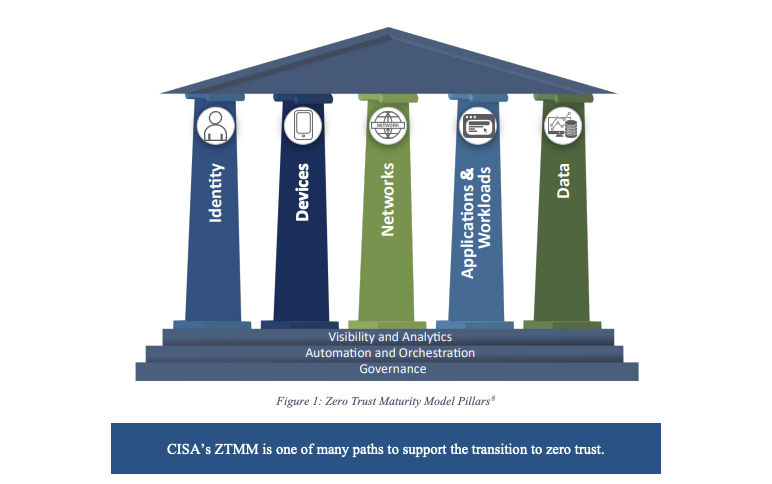
CISA's 2.0 model rests on five pillars: Identity, Devices, Networks, Applications/Workloads, and Data, each a linchpin for ZTA. I dug into these during TMF proposal reviews, and they shaped how we scored cybersecurity bets:
- Identity: Beyond passwords, CISA pushed multifactor authentication (MFA) and behavioral analytics. I saw proposals leaning on Okta or Azure AD, but the winners integrated continuous validation, think real-time risk scoring via NIST 800-207's Policy Enforcement Points (PEPs).
- Devices: Endpoint sprawl was a killer. CISA demanded visibility and compliance checks. Standouts used tools like CrowdStrike or Microsoft Intune, tying device health to access decisions, a must for ZTA's "never trust, always verify" ethos.
- Networks: Segmentation was king. Microsegmentation via VMware NSX or Cisco Secure Workload caught my eye—proposals that isolated workloads reduced blast radius, aligning with OMB's encryption mandates.
- Applications/Workloads: Secure access wasn't enough; runtime monitoring mattered. I flagged projects using AWS GuardDuty or Kubernetes RBAC to harden cloud-native apps, crucial for TMF's High-Value Asset (HVA) focus.
- Data: Encryption and categorization were non-negotiable. Proposals leveraging Boldon James or Titus for data classification, paired with NIST 800-53 controls, stood out, especially for citizen-facing systems.
My technical takeaway? ZTA's strength lies in integration. A proposal acing Identity but ignoring Networks was a house of cards—CISA's pillars demanded cohesion, and I pushed teams to prove it with architecture diagrams and test metrics (e.g., mean time to detect breaches).
TMF's Role: Funding the Unfunded
At TMF, we'd just received a $1 billion boost from the American Rescue Plan Act of 2021—a godsend for agencies sidelined by appropriations gridlock. I evaluated 120+ proposals, and ZTA projects stood out—20% targeted cybersecurity, many citing CISA 2.0. Without TMF, these efforts would've languished. Take one agency: their legacy VPN choked under remote work; their ZTA pivot—microsegmented networks and MFA—needed $10 million upfront. Appropriations couldn't deliver, but TMF did, slashing deployment from 18 months to six.
Yet, demand outstripped supply. For every funded ZTA upgrade, three sat unfunded—critical systems left exposed. TMF's revolving fund model, meant to recycle repayments, was faltering; early leniency on returns hadn't solidified into discipline. I argued for stricter ROI metrics—think reduced incident costs or uptime gains, to prioritize ZTA winners, but consensus lagged.
Lessons from the Maze
Collaborating with CISA sharpened my instincts. Their 2.0 model wasn't just a checklist—it was a stress test. I grilled proposal teams on pillar alignment, rejecting vague buzzwords for hard specs (e.g., "How's your PEP latency?"). One insight? ZTA's data pillar exposed gaps—agencies lagged on inventorying sensitive assets, a prerequisite for NIST's dynamic policies. I'd nudge TMF toward tools like Haystack or Axonius next time, visibility first, controls second.
Another lesson: culture trumps tech. Agencies with siloed IT crews stumbled; those with cross-functional buy-in—CIOs, CISOs, devs—thrived. I briefed the TMF Board monthly, advocating shared services (e.g., GSA's FedRAMP-aligned ZTA stack) to scale CISA's vision, but adoption was patchy.
Why CISA 2.0, and TMF, Matter
CISA's 2.0 model isn't perfect, it's dense, and maturity stages (Initial, Advanced, Optimal) feel aspirational for cash-strapped agencies. But it's a lifeline, grounding OMB's mandates in actionable steps. TMF amplified it, funding ZTA when traditional channels stalled —think VA's identity overhaul or USDA's network segmentation. Without that $1 billion, 2022's cyber posture would've been bleaker.
If I were coaching TMF's next wave, I'd say: Lean into CISA 2.0. Fund ZTA holistically, don't cherry-pick pillars. Push agencies to baseline their data (NIST 800-160 helps). And for TMF? Tighten the purse, tie dollars to breach reduction or citizen trust metrics. Zero Trust is a maze, but with CISA's map and TMF's fuel, we're not blindfolded anymore, we're just learning to run it faster.